Credentialitis
A semi-clinical exploration of a fully out-of-control problem.
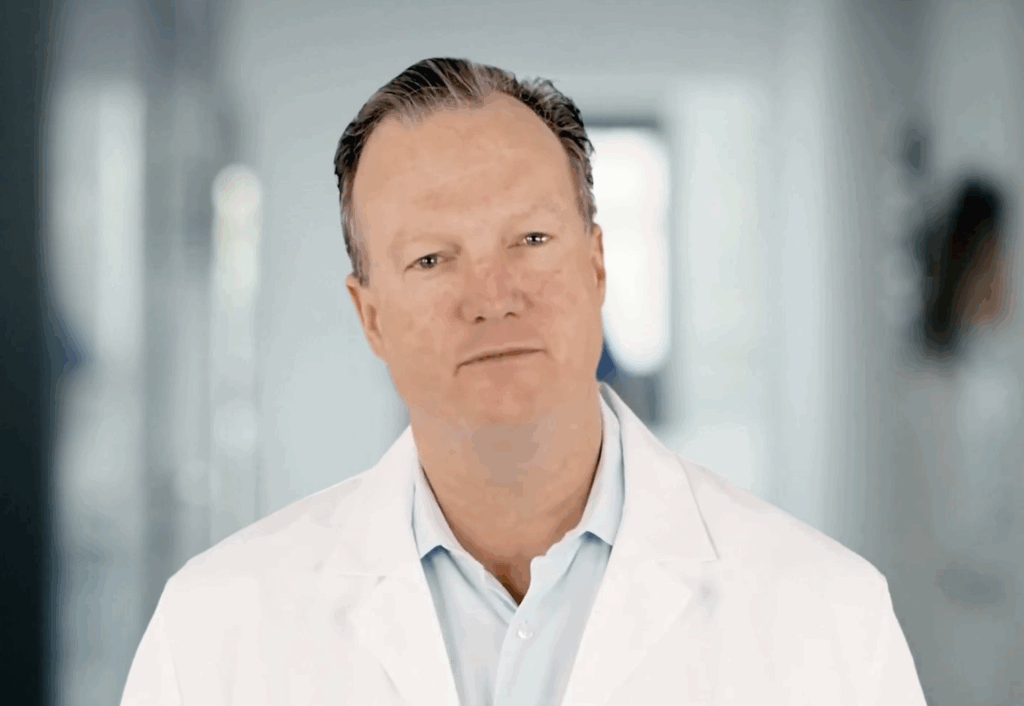
Seymour Keys, MD, PHD
Disclaimer:
Dr. Seymour Keys is not a real doctor (but he does diagnose messy IT infrastructure). Credentialitis is not a real medical condition — just a very real security and efficiency problem.
“A diagnosable condition marked by secrets sprawl across agentic AI and non-human identities — leading to operational drag and security risk.”
Before Credentialitis began spreading, humans endured another chronic identity dysfunction: Passphoria, the long-standing illusion that passwords were enough to protect users and the systems they touched. Unless you’ve developed actual amnesia, you now know they weren’t.
[Skip to the screening tool]

The harder organizations pushed for better password hygiene, the worse things got. Workers reused credentials, stored them in spreadsheets, and – most famously – stuck them to monitors on Post-it notes. Rotation policies became resented rituals. Fatigue set in. And attackers capitalized.
Security teams responded with password managers, MFA, SSO, and IAM, bringing order to the chaos of human authentication. The side effect? Password resets dropped, onboarding got easier, and support tickets stopped piling up. Then something peculiar happened: End-users became happier and more productive.

Now, unfortunately, the same pattern is playing out again – just deeper in the stack and across far more identities, especially as agentic AI takes center stage and demands access management too.
Credentialitis is simply the next stage of Passphoria. Non-human credentials may not be taped to a computer monitor, but they’re hardcoded in Git, passed through CI/CD pipelines, or buried in config files no one audits — creating security risks and saddling developers with the need to hand-roll auth that’s error-prone, tedious to maintain, and prone to leaks.
The sticky note hasn’t gone away – it’s been abstracted.
Are You Suffering from Credentialitis?

Read on to scan the companion ailments, symptoms, causes, and risk factors, take a diagnostic exam, and explore recommended treatments.
JUMP TO
Overview
Credentialitis is a chronic condition caused by over-reliance on static secrets, sprawling vaults, and dev-coded auth. It’s triggered by unmanaged non-human identities – including applications, scripts, AI agents, services, and other software workloads – that access sensitive resources without proper oversight, authentication, or policy enforcement.
It disproportionately affects:
- 🧑💻 Developers
- 🏗️ DevOps and Platform teams
- 🛡️ Security practitioners
- ☁️ Especially in cloud, hybrid, or multi-vendor environments.
Clinical Breakdown

🧪 Symptoms
- Overprivileged service accounts.
- Lingering or orphaned credentials.
- Broken CI/CD auth.
- Endless Slack threads about secrets.
- Cross-team finger pointing over access issues.
🧬 Causes
- Static secrets in code, configs, and repos.
- Lack of visibility into who/what is using access.
- Manual key rotation and vault mismanagement.
- No centralized policy enforcement for non-human identities.
⚠️ Risk Factors
- Multi-cloud and hybrid environments.
- SaaS-heavy architecture.
- Rapidly scaling DevOps velocity.
- Legacy service accounts and long-lived credentials.
❌ Failed Treatments
- Buying “another vault.”
- Writing scripts to rotate credentials.
- Relying on shared spreadsheets to track access.
- Hoping secrets scanning and NHI discovery tools catch everything.
- Praying to the IT gods (rare).
✅ Recommended Treatment
Implement non-human IAM with:
- Native workload identity
- Policy-based access
- Secretless authentication
- Centralized visibility and audit
Conditions Linked to Credentialitis:
Rotator’s Elbow
Chronic pain from the repetitive strain of manual credential rotation.
Symptoms include:
- Rotation scripts no one wants to own — but everyone blames.
- Quarterly “credential fire drills” with no institutional memory.
- Secret-tracking spreadsheets (that are, ironically, secrets themselves).
- Broken workflows triggered by someone “doing the right thing.”
Token Fatigue Syndrome
Exhaustion from managing short-lived tokens across too many clouds, services, and pipelines.
Symptoms include:
- Daily alert snoozing for token expiration warnings.
- A Jira graveyard labeled “token automation – someday.”
- Mystery 401s that vanish after restarting the container.
- Growing acceptance that auth = “just retry and hope.”
Lower Stack Strain
Bothersome back pain from embedding brittle auth logic deep in the codebase.
Symptoms include:
- Stiff, inflexible code that resists refactor.
- Sharp pain anytime a ticket mentions identity.
- Groans at “just wire up the auth real quick.”
- Architecture collapse risk from fragile trust assumptions.
Other Conditions Often Co-Occurring:
Hardcoded Dependence Disorder (HDD)
Secrets and tokens embedded in code, configs, and environments — left to rot, rarely rotated, and easily leaked.
Federated Access Disorder (FAD)
A cross-cloud dysfunction marked by duplicated roles, mismatched trust, and inconsistent access policies between identity providers.
Agentic AI Phobia
A degenerative condition where no one remembers why the AI agent exists, what it can access, or who owns it — but no one dares delete it “just in case.”
Successfully treating Credentialitis without fully addressing the root problem can lead to
Lingering Complications:
Post-Traumatic Secrets Disorder (PTSD):
Persistent stress triggered by past breaches, exposed tokens, or failed secrets management efforts.
Symptoms include:
- Flashbacks to fire drills, botched rotations, and production outages caused by expired or misused credentials.
- Slack threads titled “Does anyone know what this token is for?” — with no replies, just quiet dread.
- Security still scarred by the breach report — DevOps still haunted by the 3 a.m. token swap.
- Lingering blame and silence between teams that once scrambled side by side.
Diagnostic Quiz
Got Credentialitis? Let’s find out.
This diagnostic assessment reveals just how bad the secret sprawl is—and how to get ahead of it.
Sign up to receive the latest news from Aembit!