Eliminate hard-coded and long-lived credentials – and build truly resilient software deployment pipelines – with a unified identity system across clouds.
Identity & Access Management
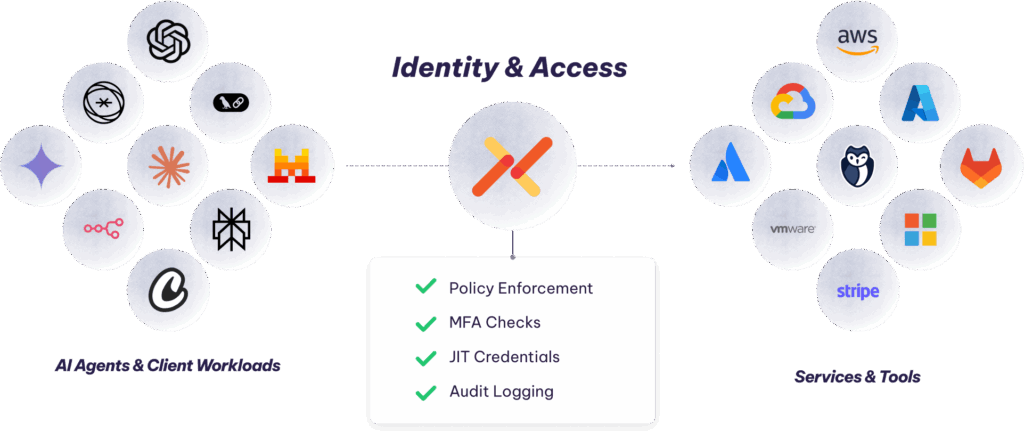
Aembit enforces access to your sensitive data and accelerates your AI use with confidence. Apply policy, context, and audit to all agent interactions based on their unique identities.
“Thanks to Aembit, we get to focus on development”
Save for each dev team
Managed agents and worklod identities

“Thanks to Aembit, we get to focus on development”
Save for each dev team
Managed agents and worklod identities
AI isn’t a human and its access can’t be effectively managed the same way. With Aembit, you get continous identity verification, run-time policy enforcement, and context-based access controls for apps, services, and AI agents. Get a centralized control point for all of it.
Aembit provides identity and access management for agentic AI and other workloads at the speed of development: no more half-finished open source identity tools or complex, fragmented vaults.
Aembit transparently provides access control. That means devs don’t need to code auth, and security can confidently provide access to resources with lower risk.
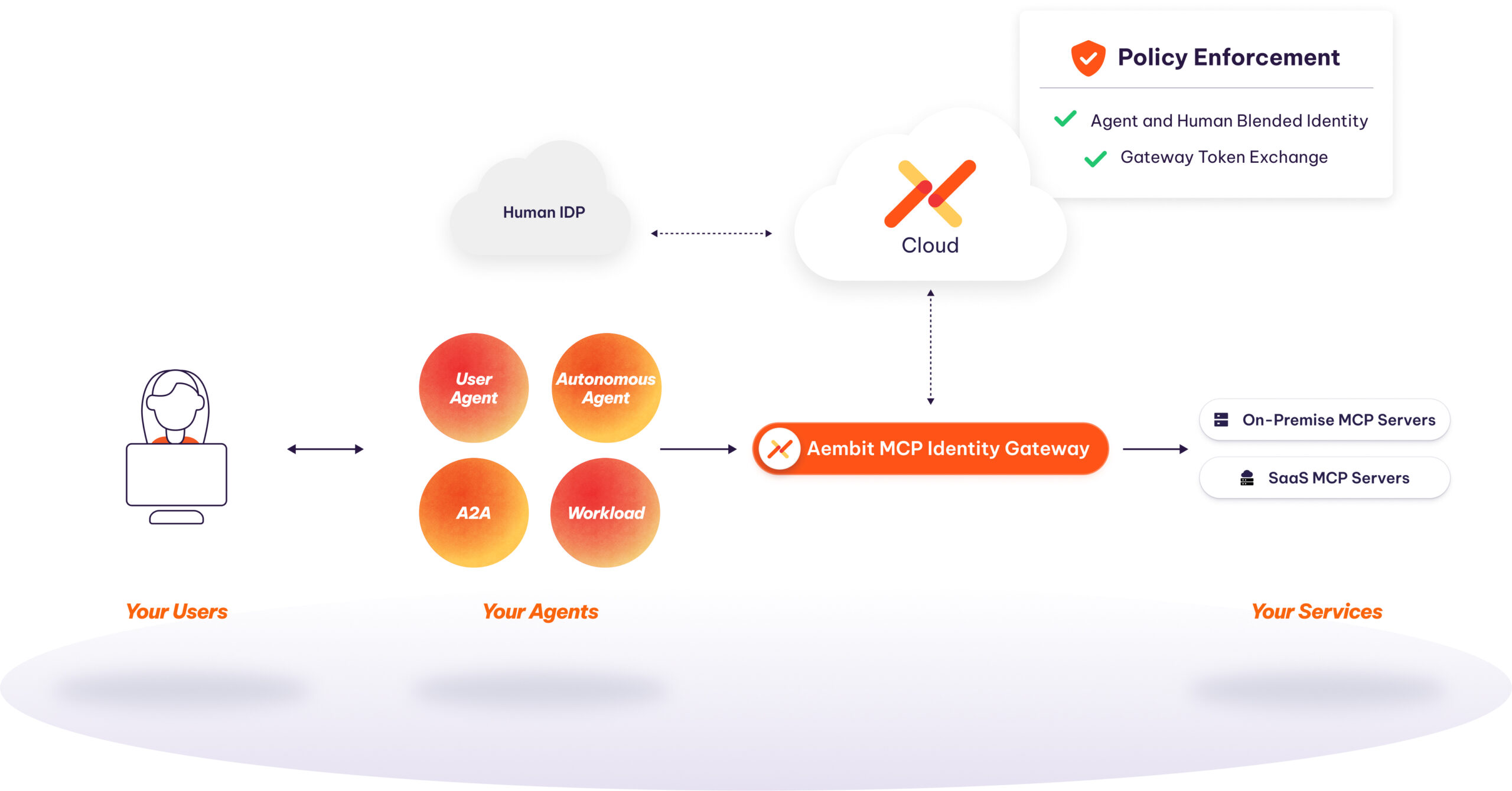
Stop AI access with a click of a button. Audit access in real-time — based on the agent’s unique identity, even if it’s operating on behalf of a user.
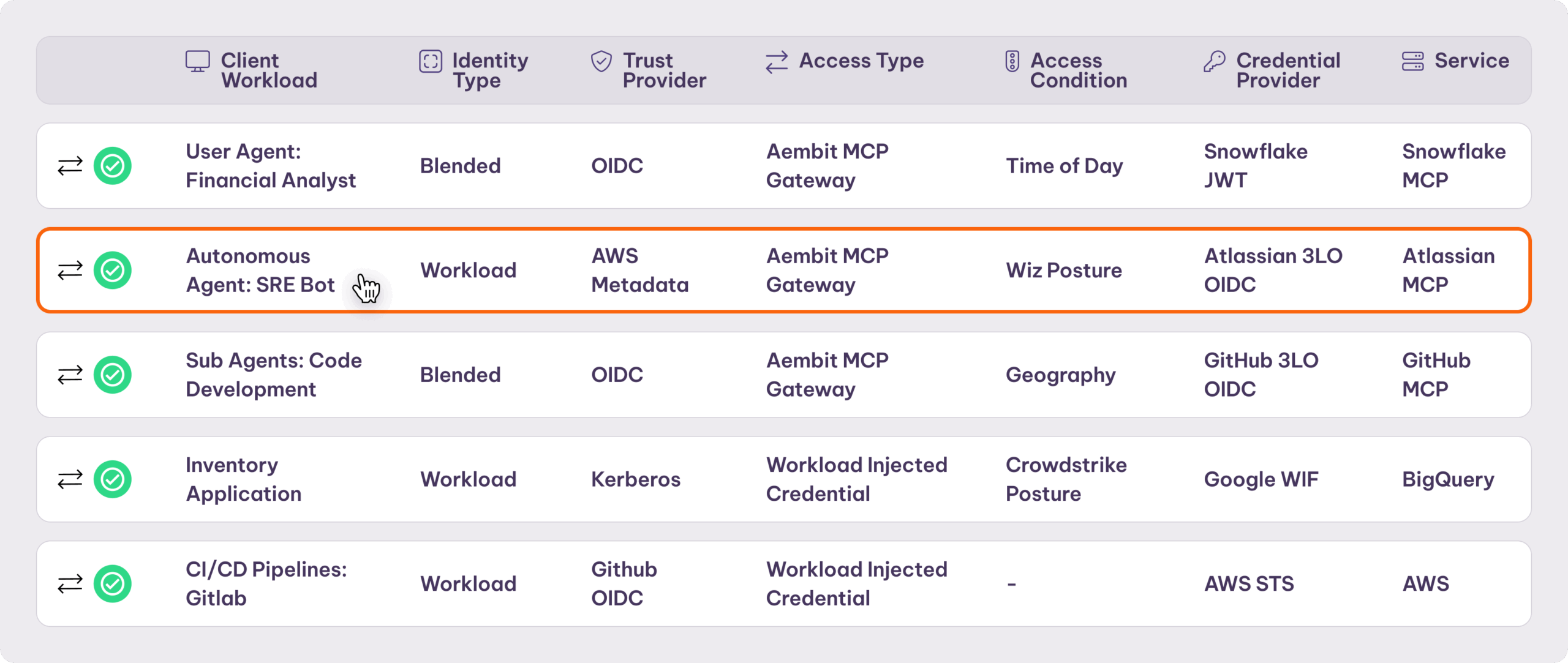
Works with MCP, A2A, & custom frameworks. Use Oauth, OIDC, SPIFFE, Kerberos, and more. Flexible authentication across AWS, Azure, and GCP, On-prem and SaaS — without deploying new identity systems.
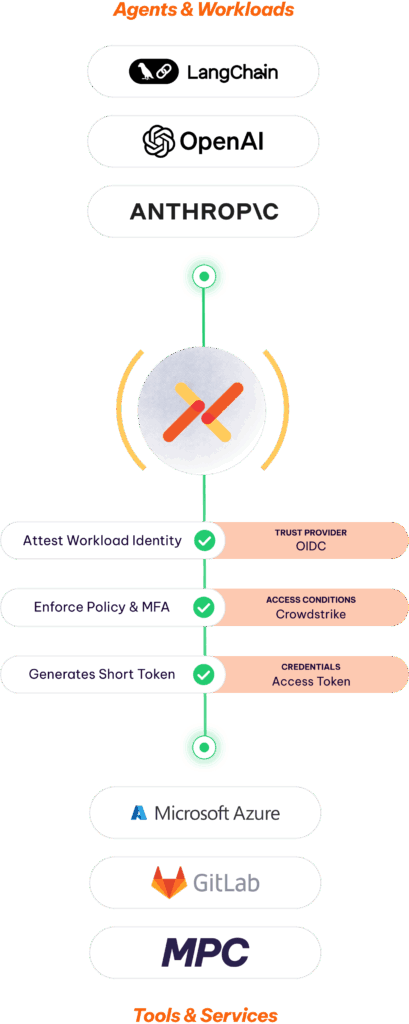
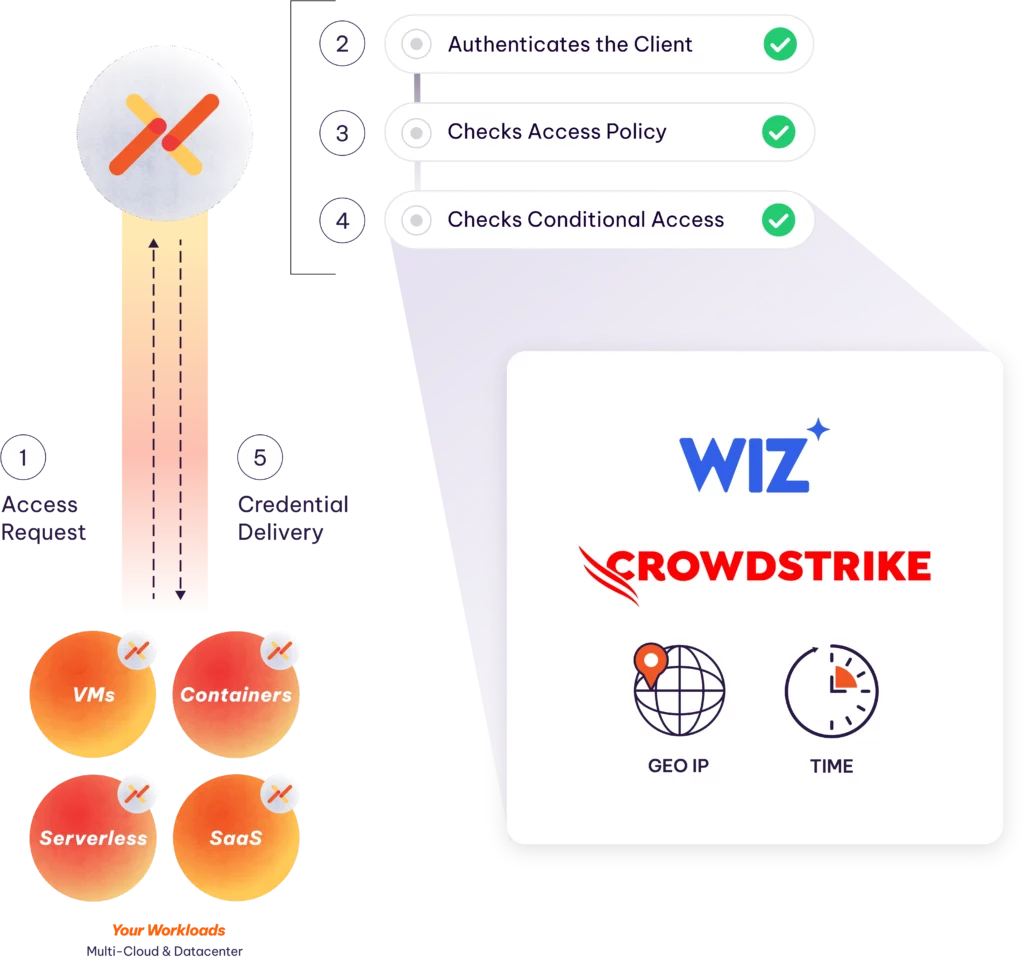
Access based on an agent or workload’s identity whether it is delegated, autonomous, or chained. No bootstrap secret, no stored secrets and no new certificates to rotate.
Define what AI agents can access with policies + MFA for agents + dynamic context. Access enforced in real-time and per-task: no scripts, no manual workflows, no surprises.
SaaS-delivered, SOC2 and ISO27001 certified. Highly available, reliable, and scalable. We don’t require dozens of add-ons and extensions for basic functions. Built and supported by a dedicated global team.
No more manual provisioning and management of secrets. Offload rotations and audit. Eliminate auth coding while giving security visibility into AI access.
Aembit replaces long-lived credentials with temporary, just-in-time access rights with per-task, contextual auth. No risk of secret leakage or unauthorized access.
Works in any cloud, across SaaS, even on-prem. Multiple auth types, a range of credential types, and no management. Aembit lets devs get back to work.
Use policies to ensure that only verified AI agents can access sensitive data and infrastructure. Stop access with a click.
Provide a single source of intelligence to verify when an agent accessed data. Prevent AI actions being hidden in user delegation.
Support billions of transactions. Automate across complex enterprise environments. Meet the toughest compliance requirements. Today.


“Agentic AI was driving our search for a secure way to control non-human access. Aembit is a step ahead – they solved this elegantly at enterprise-scale.”

“Aembit is a game changer! Along with making us more secure, Aembit also helps automate existing processes. We estimate that Aembit can save us five to 10 hours a day.”

“Securing workload identities is the foundation of a secure by default approach to security. Aembit provides an elegant approach that works across clouds, containers, APIs and SaaS services.”

“Identity is the cornerstone of zero trust. Today robust workload IAM is out of reach of all but the most sophisticated organizations. Aembit is democratizing workload IAM for all enterprises.”
FEATURES
Aembit is an independent identity broker that can secure access for AI agents, MCP servers, and workloads among clouds, SaaS, and on-premise data centers. It’s one central place to enforce & audit access from agents to sensitive resources.
Manage agentic AI access to MCP through a single, auditable data plane. Combine Agent+User into a Blended Identity , combined with the real-time policy enforcement, token exchange, and credential isolation of the Gateway.
Don’t allow agents or workloads to store or share secrets. Instead, use Aembit to deliver a secret just-in-time, per task, and without developer overhead.
Dynamically enforce access rights based on real-time evaluations of AI Agent security posture, geography, time windows and other key behaviors.
See exactly what AI agents and workloads access – not hidden behind users or their parent agents. See everything based on each agent’s unique identity.
Streamline and secure access from AI agents to leading LLMs like OpenAI, Claude, and Gemini, APIs, and tools with policy-based, identity-driven controls.
The explosion of Agentic AI is posing new challenges for security and DevOps teams across all industries and organizational sizes.
Eliminate hard-coded and long-lived credentials – and build truly resilient software deployment pipelines – with a unified identity system across clouds.

“Aembit is a rising star in the Non-Human Identity and Access Management space, offering an innovative approach to securing workload identities. Its focus on secret less authentication, dynamic access control, and Zero Trust principles makes it a strong contender in this emerging market.” Read more
Get started in minutes, with no sales calls required. Our free- forever tier is just a click away.