Why AI Agents Need Identity and Access Management
AI agents handle real work: looking up customer data, creating tickets, summarizing logs, and even triggering changes in your cloud infrastructure. Agents need access to your most sensitive data and critical systems to be useful. Just like humans, access is the first line of defense, and who agents are determines what they can do. Most enterprise guardrails were built for people, not for fast-moving software actors that spin up for seconds, act independently, and chain across tools.
With the speed of AI adoption, friction is rising: security teams can’t meet compliance and risk requirements, and development teams take on overhead to implement authentication when they want to ship features.
Aembit IAM for Agentic AI gives security teams a way to responsibly provide and revoke access to sensitive data and resources based on agent identity and centralized policy. And since Aembit is no-code, security teams can reduce identity security overhead on development teams.
AI Access Problems Enterprises Face
No clear identity for the agent. Today, an agent’s access is often hidden behind a human’s identity, both in actions and the audit trail.
Secrets in the wrong places. Where agents use machine credentials, teams reach for the simplest (and least secure) form of access: secrets and API keys. If a key lands in the agent’s runtime, the agent can use it, pass it to others, emit it, and lose it to anything that touches that runtime.
Human processes don’t map. Joiner/Mover/Leaver and monthly rotations assume employees, not jobs that begin and end in minutes. Plus, human MFA doesn’t work for AI agents.
Everything speaks something different. Agents speak MCP; targets speak OIDC, OAuth2, PATs, SSH certs, API keys, or database logins. Bridging that safely is hard. It drives developer overhead and weak accountability.
Boundaries everywhere. Agents in one cloud routinely need to access SaaS and on-prem systems in another trust domain, each with different identity systems, policies, and credentials.
Auditing and attribution gaps. Without a distinct agent identity (and user context when present), logs collapse actions under a human’s token or “some agent.” That undermines compliance, incident response, and root-cause analysis.
Why This Matters Now
Pilots are becoming production. Leaders want efficiency; security and compliance need provable control. If you can’t allow access safely, you end up blocking broadly.
Early incidents are access failures. They include unclear attribution, unscoped data pulls, stale tokens used by “some agent” and weakening of controls to just make access work.
Security can block or enable. AI is moving. Security can enable developers with confidence or slow adoption.
The 5 Requirements of IAM for Agentic AI
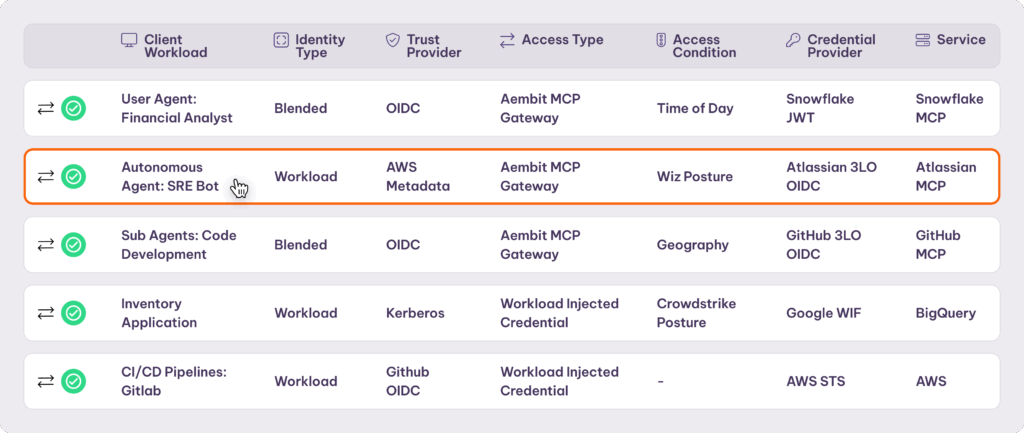
Working with real customers (a Fortune 250 retailer, a top government security contractor, a leading AI agent platform, and a highly regulated financial services company), Aembit formed a clear view of what enterprises need to protect data and systems in agentic workflows.
Aembit combines two core capabilities, blended identity for AI agents and an MCP Identity Gateway, with an enterprise-class Workload IAM foundation to achieve five things:
Treat the agent as a first-class, distinct identity, and add user context when present. Use the agent’s environment to provide dynamic identity and conditional access at the scope, scale, and velocity of agents. Bind upstream human context when the agent acts for someone.
Enforce runtime access at a clear control point with a well-defined policy and issue secretless, just-in-time credentials that expire quickly.
Enable a kill switch so security can quickly revoke access if an agent behaves erratically.
Translate credentials safely across SaaS, cloud, and on-prem targets without exposing creds to the agent.
Provide clear attribution within audit logs, per agent, per user binding, per tool, without downstream rewiring.
Aembit issues ephemeral credentials after policy evaluation. No long-lived keys sit in code and no vault lookups run in agents. Access is short-lived and configurable. Policies translate across clouds, data centers, and SaaS. You get one control point for modern and legacy protocols. Developers get a zero-code path to secure access; security teams get zero standing privilege with full auditability.
How Aembit Solves IAM for Agentic AI
Two challenges define agent access in enterprise AI deployments:
How do you give an AI agent an identity dependent on both the agent software and the human interacting with it?
How do you provide least privilege along the entire access chain, so the agent and the MCP server have only what they need?
Aembit addresses both with Blended Identity and an MCP Identity Gateway.

Blended Identity: A First-Class Identity for the Agent, With Upstream Human Context
Agents act for people but are not people. Blended Identity gives each agent a first-class non-human identity, then optionally binds a user context so access can be scoped and audited with attribution. Our design treats the agent as its own workload identity, then binds upstream human context when the agent acts on someone’s behalf.
Outcomes
Ability to enforce an access policy based on the blended identity. Each policy enforces least privilege authorization based on the blended identity of the agent and the user.
Attribution that distinguishes an agent acting for a user from a user acting directly.
How It Works: MCP Authorization Service and Human IDP Integration
When an agent (in container, VM, function) requests access, Aembit dynamically attests to workload identity via cryptographically verifiable documentation from the environment (e.g., AWS metadata document, Kubernetes service account token, OIDC token, Kerberos ticket). Agents never handle bootstrap secrets. This removes the “Secret0” problem entirely.
For user-driven agents, where the agent receives directions via a user interaction, we bind the agent identity with optional user context: the authenticated human (IdP claims, group/role attributes, purpose-of-use, ticket ID). Additional context comes via conditional access attributes: execution metadata (agent posture, time of day, geography), and tool name, model, chain step, or other risk signals.
When user context is present, we propagate only the minimum required attributes downstream to define scope. Every access log includes both agent identity and, if available, user_context so audits can always tell “agent acting alone” vs. “agent acting for Alice.”
Two elements power blended identity:
- An MCP authorization service within Aembit, whereby customers can redirect their on-premise or SaaS MCP servers to use Aembit for authorization with a line of configuration.
- Integrations with human IDPs, where we pull context on humans, groups, and roles. Aembit focuses on the identity and policy to control access for the agent or workload. We consume data from your workforce IDP and bind it to the agent’s operating context.
MCP Identity Gateway: Identity-Aware Termination and Token Exchange
The MCP Identity Gateway splits the access flow into two phases: authenticate the agent and user and issue a blended identity credential that the agent uses to authenticate to the gateway. The gateway uses token exchange to obtain the correct access credential for the target and returns that credential to the MCP server to access the service. The agent never receives the access credentials. This model works for both enterprise-owned custom MCP servers and third-party SaaS MCP servers.
Policy evaluation: Before any MCP tool call executes, Aembit evaluates policies against the blended identity and run context (resource, parameters, time, geo, risk). If allowed, it proceeds; otherwise, it blocks and records a structured denial with reasons.
Token exchange: When Aembit attests to the agent identity, it issues an identity credential usable only at the gateway. The gateway, working with Aembit Cloud, exchanges it for the exact access credential the target expects, short-lived and audience-scoped when possible.
Examples: Mint an OIDC access token for a SaaS API with claims reflecting user department + agent role; generate a temporary DB login; produce a one-time PAT/API key for legacy tools that can’t consume OIDC.
What This Enables
Policy-enforced access, with just-in-time credential delivery: The agent never sees or stores long-lived credentials; nothing sits in files, env vars, or prompts.
Cross-boundary access that “just works”: An agent in AWS can call an MCP tool that hits Snowflake, Salesforce, or an on-prem DB, each with the right ephemeral credential and least-privilege scope.
Provable attribution: Every tool call is bound to who/what/why at the moment of use. The upstream context (human or another agent) is fully traceable.
Better Together: Blended Identity + MCP Identity Gateway
While the MCP Identity Gateway is essential for securing third-party tools, it delivers its strongest security architecture when combined with our MCP Authorization Service for your own applications.
In this model, you configure Aembit as your Authorization Server and write a simple policy: “Only issue access tokens to the MCP Identity Gateway.” This forces all traffic, internal and external, through a single, auditable data plane. You get the user context of Blended Identity combined with the real-time policy enforcement, token exchange, and credential isolation of the Gateway in one unified flow.
Workload IAM Foundation: Policy, Enforcement, and Auditable Runtime Control
Your AI stack is only as powerful as the data it can access. That data lives in distributed, heterogeneous systems built on existing patterns. An AI-native access platform must understand these patterns.
Under the covers, these capabilities build on the hardened Workload IAM fabric Aembit runs at scale for non-AI workloads, redesigned for agentic patterns.
Central Policy Plane, Distributed Enforcement
Policy enforcement using attributes from the agent, resource, and environment. Enforcement happens at the host/cluster edge via our transparent proxy/sidecar for zero-code adoption or in-process via lightweight SDK. The MCP Identity Gateway also serves as an enforcement point.
Zero standing privilege (ZSP): Access is granted only at request time, after policy evaluation, materialized as a short-lived credential with pinned audience, scope, and TTL.
Conditional access (like MFA, but for agents): Policies can require stronger attestation of the agent runtime (signed image, security posture, geolocation).
Kill switch: Block specific agents with a simple policy change; with short-lived credentials, blocking is nearly immediate.
Unified audit with attribution: Every decision (allow/deny), JIT credential issuance, and downstream call is a structured event tied to the agent and optional user context. These records power compliance (SOC 2/ISO), incident response, and granular cost/usage analytics.
Developer and Ops Integration
Zero-code on-ramp: Drop in the host-based proxy; we intercept, identify, and enforce.
CLI and SDK options: For scripted agents or where you want explicit calls, the CLI and SDK provide the same identity bootstrap and JIT flows.
Heterogeneous environments: Works across Kubernetes, virtual machines, serverless functions, laptops (for local tools), and hybrid networks.
Varied authentication protocols and credential types: OAuth, Amazon/Google/Azure short tokens, JWTs, API keys, username/password, SPIFFE, for example, are supported. And the list keeps growing.
Enforcement, visibility, and developer simplicity work together here. That combination is what makes IAM for agentic AI and workloads effective at enterprise scale.
Accelerate AI Adoption Confidently
IAM for agentic AI protects enterprise resources and unlocks what agents can do for the business. When security teams can confidently secure agent access, organizations can innovate and explore what agents make possible. Aembit gives enterprises:
- A central runtime control point to allow, constrain, or kill AI access without chasing secrets across agents, tools, and clouds.
- Agent velocity (no auth code, no key wrangling) with least-privilege, zero-standing-privilege guarantees.
- Auditable attribution for every action, unified across agentic AI and existing non-AI services, one model, consistent controls.
As AI agents take on more responsibility inside enterprise environments, identity becomes the control plane that determines whether those agents operate safely or become a liability. Aembit’s Workload IAM platform provides that control plane, from agent identity through credential issuance to full audit trail, across every cloud, SaaS platform, and on-prem system your agents touch.
Related Reading
Ready to Try Aembit?
Get started in minutes, with no sales calls required. Our free- forever tier is just a click away.