Case Study
A $300B Investment Firm Secures Claude Access with Aembit
Aembit is the identity control plane securing this firm’s Claude deployment across all connected MCP servers — full identity, access control, and audit logging in place for every employee, with financial analysts and executives as the first critical use cases.
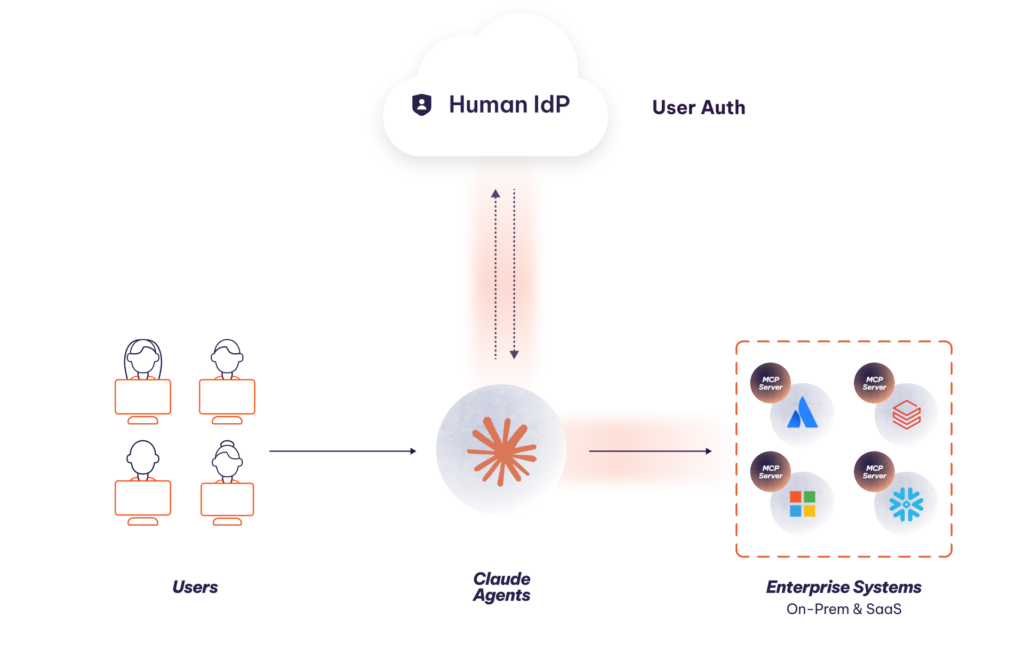
No agent identity, only user identity.
Long-lived credentials stored in the wrong places.
No centralized access control or auditability.
Blended human-agent
identity.
Just-in-time, secretless
access.
Run-time policy enforcement with detailed, auditable access logs.

Why the Customer Needed Aembit
This organization is using Claude to deploy personalized AI assistants across its entire workforce, giving agents access to financial datasets for research, email and calendars for productivity, and sensitive company information through SharePoint and Microsoft 365. The security team identified three critical gaps their regulated environment couldn’t accept:
- No agent identity, only user identity. When Claude accessed an MCP server on an analyst’s behalf, it did so using the analyst’s full identity and access rights — with no distinct agent identity, no audit attribution, and no coverage for services outside Okta’s governance.
- Long-lived credentials stored in the wrong places. MCP authentication required storing secrets, tokens, and API keys directly in Claude or in MCP server configurations — static, unrotated, and sitting in places never designed to be credential stores.
- No centralized access control or auditability. Policy enforcement for agent behavior was piecemeal, based on human identity, and lacked visibility into whether the human or agent took action.
What Aembit Does
- Blended human-agent identity: Aembit creates a unique blended identity based on the user and the agent enabling a unified framework and single, consistent security policy for managing both human and non-human identities.
- Run-time policy enforcement: Granular least-privilege access enforced per agent, per MCP server, within the firm’s existing Okta identity foundation
- Just-in-time, secretless access: Long-lived stored credentials eliminated; replaced with short-lived, policy-scoped tokens issued per session. No static secrets.
- Auditability based on detailed access logs: Every agent action is logged and attributed with full access logs forwarded to CrowdStrike SIEM, giving the security team the same visibility into agent behavior as human user activity
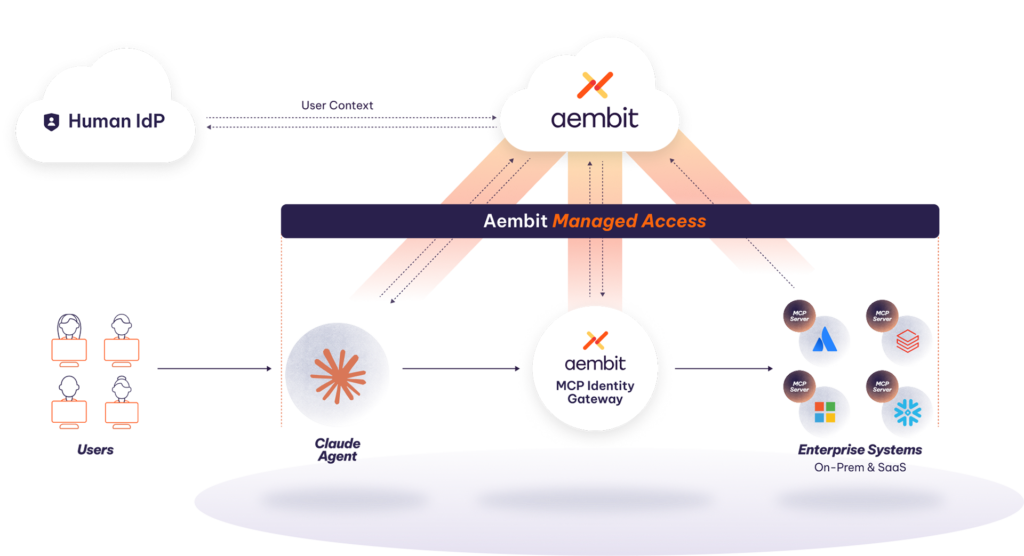
How It Works
Aembit is deployed as a SaaS service. Its cloud control plane offers policy enforcement and logging. Its MCP Authorization Service handles standards-compliant OAuth with PKCE and issues blended identity tokens, and an MCP Gateway that enforces access policy with token exchange in real time and logs every tool invocation. Human identity is anchored to the firm’s existing Okta instance. Deployment takes two weeks, with less than six hours of security team time required to stand up the solution.
What’s Next
Three expansion tracks are underway: expanding the footprint of AI agents and MCP servers covered by the existing deployment; securing agent-to-agent communication as multi-agent workflows emerge; and extending Aembit’s workload IAM beyond AI agents to CI/CD pipelines, DevOps credential management, and broader secretless access across the organization.
Related Content
Secure Claude
With Aembit’s IAM for Agentic AI
Get started today – no sales call required.