Give every Claude agent a verified blended identity, enforce exactly what it can access, and produce an audit trail that holds up to compliance review without slowing deployment.
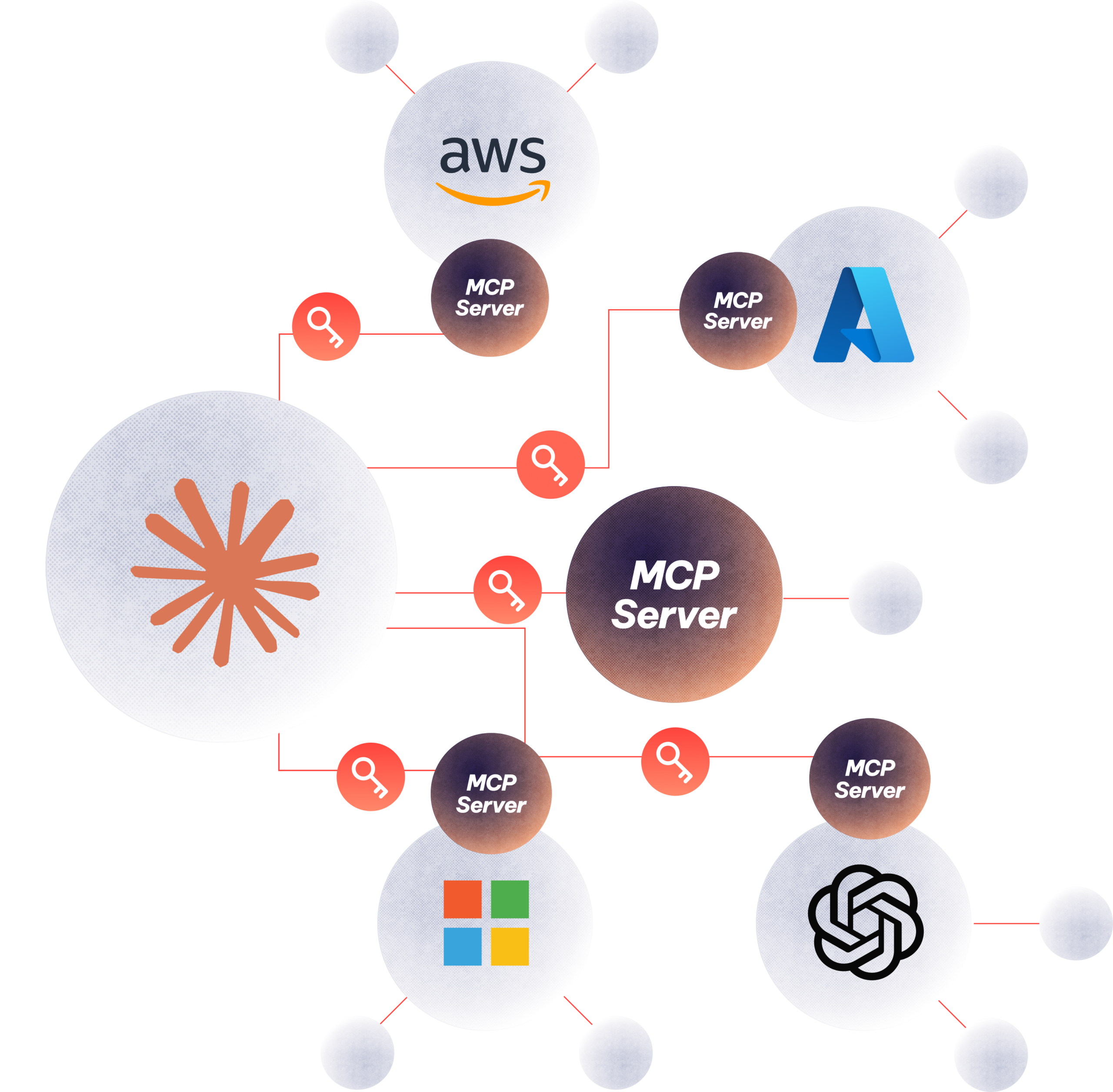
When organizations deploy Claude for Work or connect Claude to tools through MCP, a critical security gap opens. Claude operates using the employee’s full identity and access rights with no distinct agent identity, no access guardrails, and no way to distinguish Claude’s actions from the employee’s in an audit log.
Security teams need to close three security gaps to deploy Claude securely:
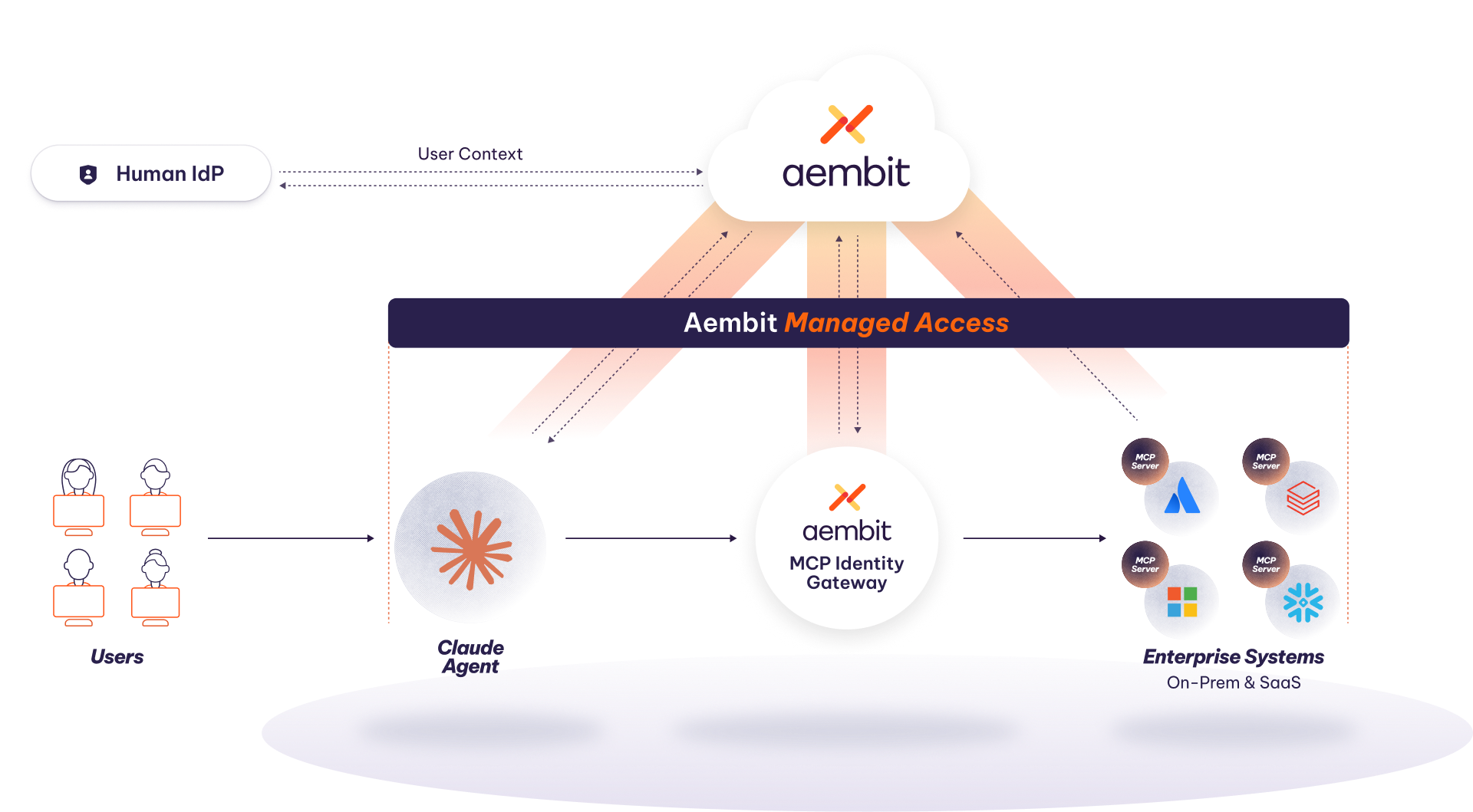
Aembit provides a central control plane that gives Claude a blended identity tied to but separate from the user’s human identity and enforces least-privilege access policy at the MCP server level in real time with complete, attributable audit record of every action Claude takes.
Security teams can say yes to Claude deployments with the same identity, access, and audit controls they apply to their human workforce.
A $300B investment firm deployed Claude across its analyst and executive workforce connecting agents to Microsoft 365, Factset, and Kensho with Aembit securing every connection from day one. Their security team went from blocking the rollout to owning it.
Govern Claude’s access to tools and resources regardless of where agents operate or which MCP servers they connect to.
Replace static credentials with ephemeral, single-use tokens.
Unified treatment of human and agent identities within the same access and audit framework.
Replace the insecure token passthrough pattern with a governed, policy-enforced brokering layer.
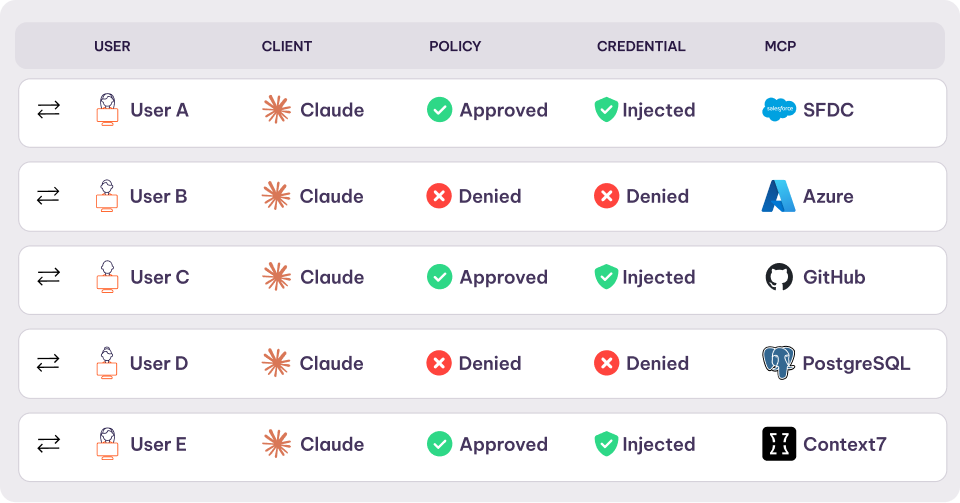
Real-time allow/deny decisions at the traffic boundary, before any tool is invoked or data is reached.
A single control plane governing all agent-to-service access policies across the environment.
Complete, human-agent-attributed logs for full operational visibility.


Turn on secure, governed access for every Claude agent without slowing down your rollout. Give your security team full visibility, enforce least-privilege by default, and ensure every action is attributable, auditable, and compliant from day one.