- Analyst Reports
Agentic Identity Access Platforms Report
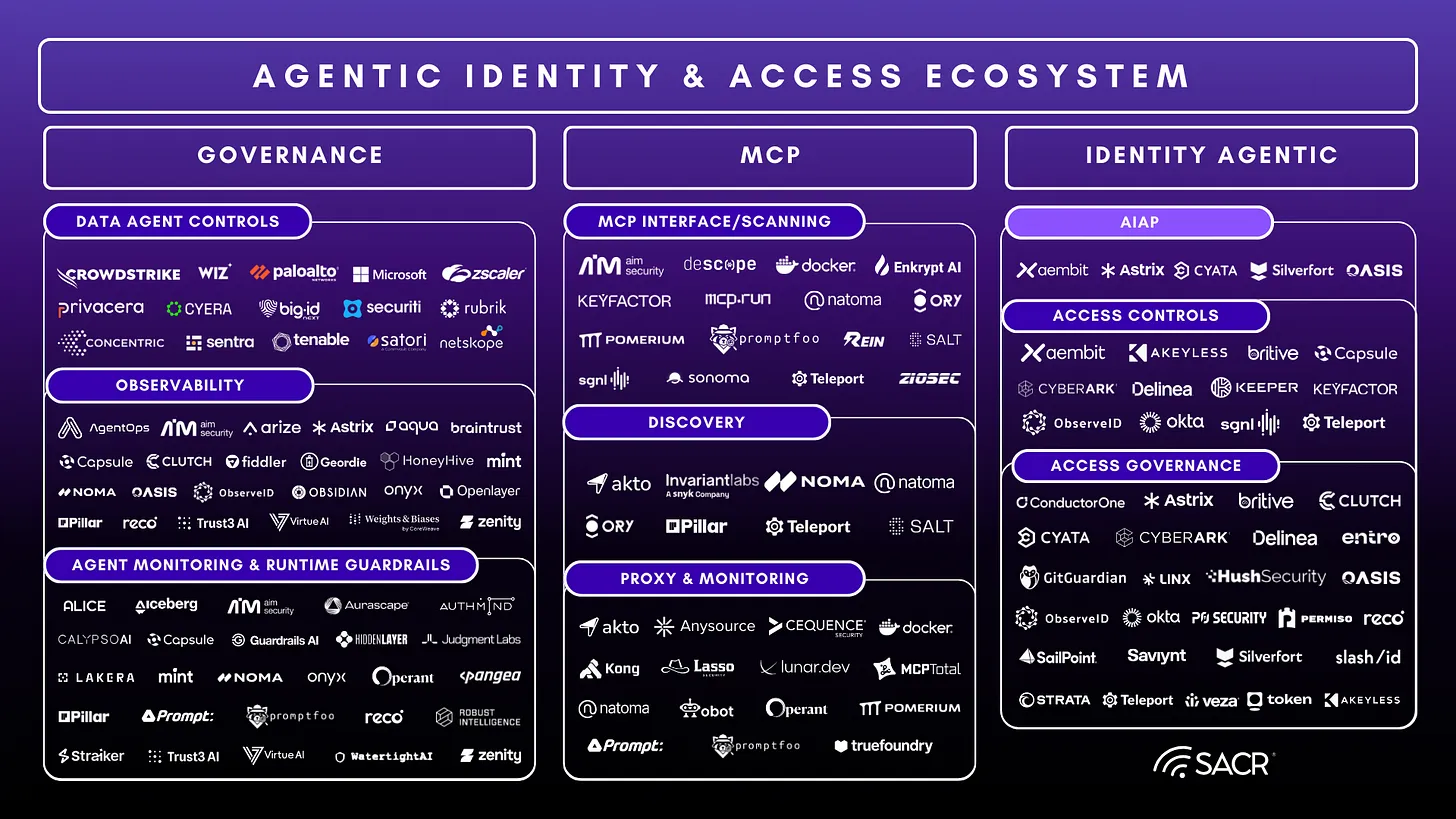
As software takes on continuous, autonomous work inside enterprises, identity and access controls built for human logins no longer hold. Agents act at machine speed, chain actions across systems, and operate with levels of access traditional IAM, IGA, and PAM were never designed to handle.
This report from Software Analyst Cyber Research examines how identity architecture is changing in response. It explains why credential-centric models break down and what an end-to-end access architecture looks like when software, not people, is doing the work.
Inside, you’ll find:
- Why legacy identity systems struggle with autonomous, non-human access.
- What Agentic Identity Access Platforms are and why a centralized broker matters.
- How intent, scope, and duration replace standing credentials and inherited access.
- A four-phase operating model covering discovery, authorization, access fulfillment, and termination.
- How Aembit implements this model in practice using brokered, short-lived access enforced at runtime.
This report is a practical reference for teams responsible for identity, access, and audit as agentic AI activity continues to scale.