At RSA Conference 2026, you could not walk more than 20 feet without hearing someone talk about agentic AI risk, non-human identity, and the need to secure autonomous systems.
But while most vendors were talking about it, Aembit was demonstrating it.
That is not a small distinction. For the past several months, customers and design partners have been running Aembit IAM for Agentic AI in alpha and beta, stress-testing it against real workflows, real MCP servers, and real enterprise security requirements.
Today, it is generally available.
AI Agents Are in Production. The Security Infrastructure Is Not.
AI agents are not coming. They are already here: calling APIs, querying databases, and triggering workflows, autonomously, at machine speed. The security controls to govern them are lagging badly.
Gartner’s February 2026 cybersecurity trends report identifies “Identity and Access Management Adapts to AI Agents” as one of six trends with broad enterprise security impact this year, citing gaps in identity registration, credential automation, and policy-driven authorization for machine actors. The field data matches: a 2026 survey of 900+ practitioners found that 80.9% of teams have AI agents in active testing or production, yet only 21.9% treat them as independent, identity-bearing entities. Most still rely on shared API keys or inherited service accounts.
New Aembit-Cloud Security Alliance data details the consequences – 68% of organizations can’t clearly distinguish between agent and human activity, and 74% say agents often end up with more access than they need. Meanwhile, 97% of enterprise security leaders expect a material AI agent-driven security incident within the next twelve months, yet only 6% of security budgets are allocated to this risk.
The core problem is identity. Agents have no workload attestation, no ephemeral credential issuance, no least-privilege enforcement. Aembit exists to close that gap.
Built on a Foundation That Was Already Solving This Problem
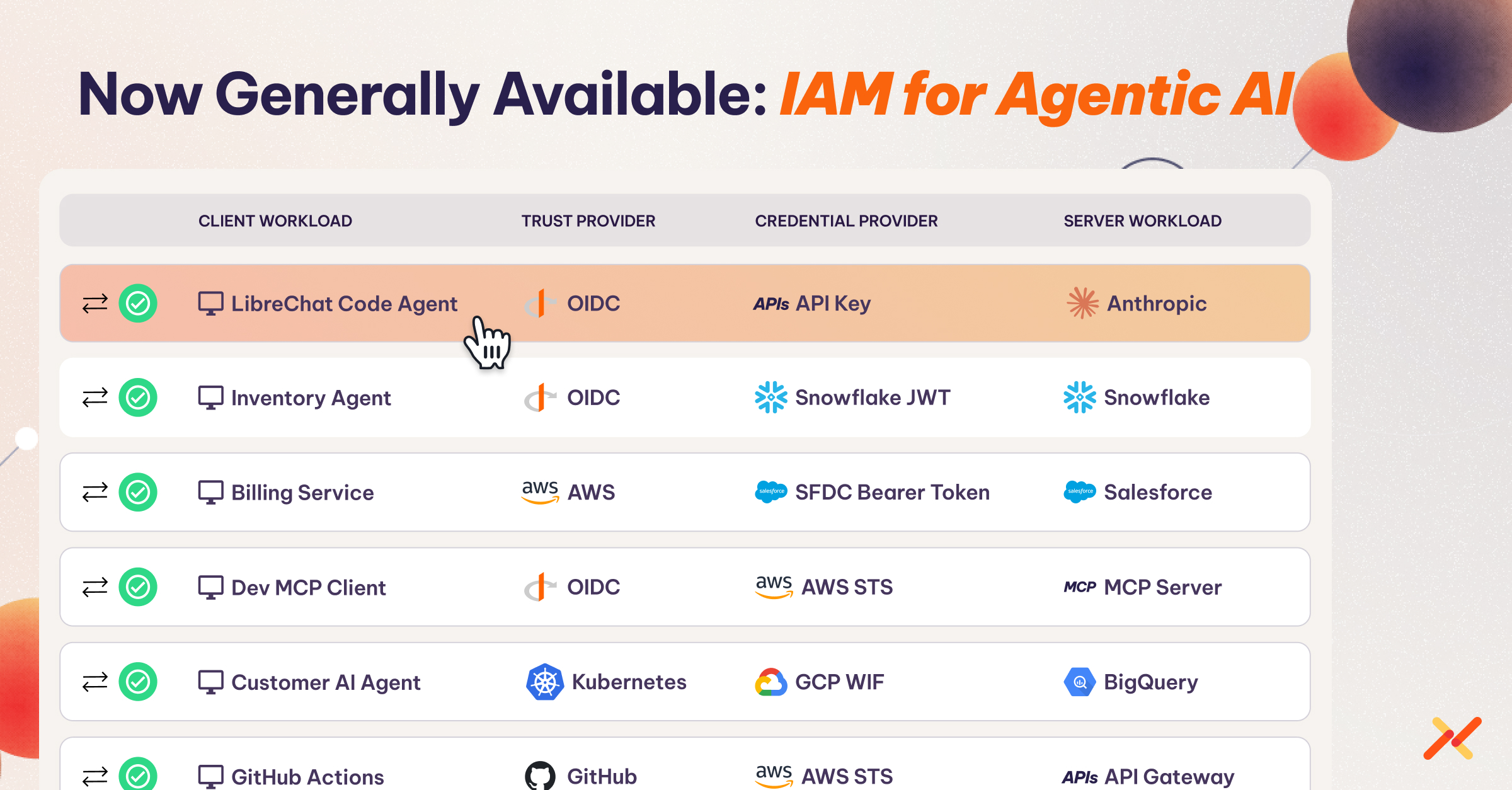
Aembit has been enabling non-human identity and workload access for several years. The architecture behind workload IAM, cryptographic workload attestation, policy-based access decisions, secretless credential exchange, and structured audit logs, is exactly the right foundation for governing AI agents too.
When AI agents started appearing in enterprise environments, we extended the same proven model to cover this new kind of non-human identity. That foundation gives Aembit something most vendors entering this space cannot offer: production-grade infrastructure that has already been running at scale, with real customers, across real enterprise environments.
Two New Components Extending Aembit’s Core Platform
Aembit Cloud is the core of the platform, providing workload IAM, policy management, access audit, and the Aembit Access Policy framework that governs all workload and agent access decisions. IAM for Agentic AI adds two new components to that foundation, purpose-built for AI agents operating over the Model Context Protocol (MCP).
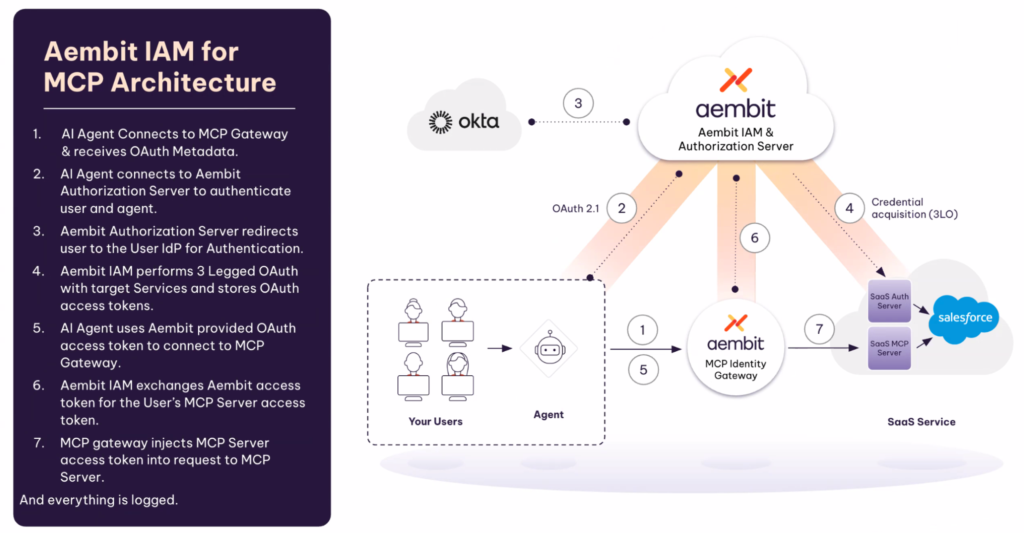
1) MCP Authorization Server
The MCP Authorization Server runs as a fully managed capability in Aembit Cloud with nothing to deploy or maintain on your end. It implements the OAuth 2.1 authorization code flow defined in the MCP specification, so AI agents and MCP clients can authenticate and receive access tokens minted by Aembit access policies, without custom authorization code. It integrates with identity providers you already use, including Okta, Azure AD, and Google, through OIDC and SAML. This is the right starting point when human users are authenticating through an AI client like Claude Desktop or Gemini CLI and you need that user context in the access decision.
2) MCP Identity Gateway
The MCP Identity Gateway deploys as a Linux virtual machine in your environment, giving you control over network boundaries and data locality. It validates tokens and enforces policy on every MCP request, then exchanges credentials on the agent’s behalf so the agent never holds direct credentials for the MCP servers or the enterprise systems behind them. It works for both custom MCP servers you host and third-party SaaS MCP servers. Containerized and fully managed deployment options are on the roadmap.
The two components work well independently and even better together. The authorization server handles user authentication and issues access tokens. The identity gateway validates those tokens on every subsequent request, enforces policy, and performs credential exchange in real time, covering the full access control layer from user login through to MCP server response.
Blended Identity: A New Access Model for a New Kind of Actor
Traditional IAM answers one of two questions: who is this user, or what is this workload? AI agents require both answers at the same time. Blended Identity is Aembit’s access model that evaluates the identity of the AI agent and the human operating it together in a single policy decision, at request time.
Without Blended Identity, organizations face a binary choice. User-only identity means every AI client gets the same access regardless of trust level. Workload-only identity means every user of an agent gets identical access with no per-user scoping. Neither model is sufficient for agentic AI access management.
Aembit asks instead: “Is this specific user, using this specific agent, authorized to access this specific resource right now?” That enables access policies enforcing, for example, that:
- Engineers can use Claude Desktop to access Jira, but only the security team can use it to access the vulnerability scanner.
- A user can access Confluence through Claude Desktop but not through an untrusted third-party agent.
- One user’s AI agent access can be revoked without affecting other users or rotating any shared credentials.
Blended Identity also enforces per-user credential isolation. When the MCP Identity Gateway connects to a downstream MCP server on behalf of two different users, each receives credentials scoped to their own identity. User A’s session uses User A’s permissions. User B’s session uses User B’s. The agent holds neither.
Every access event captures who the authenticated user was, which AI agent made the request, which resource was accessed, and what policy decision was made. That dual attribution is what makes it possible to satisfy compliance requirements including SOC 2, HIPAA, and PCI for AI agent access in a way that workload-only or user-only identity cannot.
Aembit does not replace your workforce identity provider. It consumes data from your existing IdP and binds it to the agent’s operating context, without requiring new identity infrastructure.
The Rest of the Capability Stack
Beyond Blended Identity and the two MCP components, Aembit IAM for Agentic AI includes
- Policy-based, just-in-time access so agents never hold standing credentials.
- Conditional access factors like time of day, geography, and runtime posture.
- A kill switch that blocks a specific agent immediately via policy change.
- Structured audit logs that integrate with your SIEM.
- No-code deployment path through the host-based proxy.
CLI and SDK options are also available for teams that want explicit integration.
Pricing: Three Tiers for Every Stage of Deployment
The free ‘Starter’ tier is designed for development and exploration, with enough capacity to run a meaningful proof of concept at no cost and no time limit. The ‘AI’ Teams tier, running $20 per agent per month, is for teams moving agents into production, scaling from 10 to 500 agents with live support. ‘Enterprise’ covers unlimited agents, custom log retention, conditional access, and 24×7 support for organizations operating at scale.
Full details and a feature comparison are at aembit.io/pricing.
See It in Action
We have two videos worth watching before your next architecture conversation about AI agent security. The first covers securing MCP servers with Aembit including how Blended Identity fits into enterprise security architecture, and the second covers Aembit’s partnership with Netskope to add identity and AI guardrails.
Start Scaling IAM for Agentic AI Access Today
The free ‘Starter’ tier is the fastest path to understanding how IAM for agentic AI access management works in practice, with enough capacity to run agents across development and QA before you scale to production.
You can sign up in minutes with no sales call required.
Sign up for the free ‘Starter’ tier | Talk to an engineer | Read the AI Guide docs
The Workload IAM Company
Manage Access, Not Secrets
Boost Productivity, Slash DevSecOps Time
No-Code, Centralized Access Management