Most organizations still treat credentials as something that must be protected, stored, and rotated. But a second model is quietly reshaping how machine authentication works: eliminate static secrets altogether and authenticate workloads using identity and just-in-time access. These two approaches represent different philosophies, different operational realities, and different long-term costs.
It also isn’t a binary choice. Most organizations run a mix of modern cloud workloads, legacy systems, SaaS APIs, and CI/CD pipelines. Some of those environments support secretless authentication today, while others will always require a secrets manager. Understanding where each model fits, not picking a side, is the real strategic decision.
1. Two Security Philosophies, Explained Simply
Secrets management assumes static credentials are a fundamental part of your architecture. Its job is to store those credentials centrally, protect them, and rotate them regularly. Eliminating secrets takes the opposite view. It assumes static credentials are the root of the problem and removes them from the authentication path entirely by issuing short-lived credentials on demand.
These philosophies produce two very different security and operational models.
Secrets Management
Secrets management exists to make static credentials as safe as they can be. It stores them in secure vaults, enforces access controls, rotates them on schedules, and provides auditing for compliance. When done well, it prevents hardcoded credentials, reduces the risk of accidental exposure, and protects legacy systems that cannot authenticate any other way.
This model works because it accepts the premise that long-lived credentials will exist and need to be guarded.
Secrets Elimination
Secrets elimination does not protect static credentials; it removes them. Workloads authenticate using their identity, not a password or API key. After identity is verified, a short-lived credential is issued for that specific task and expires quickly after use. No static credential sits around waiting to be stolen.
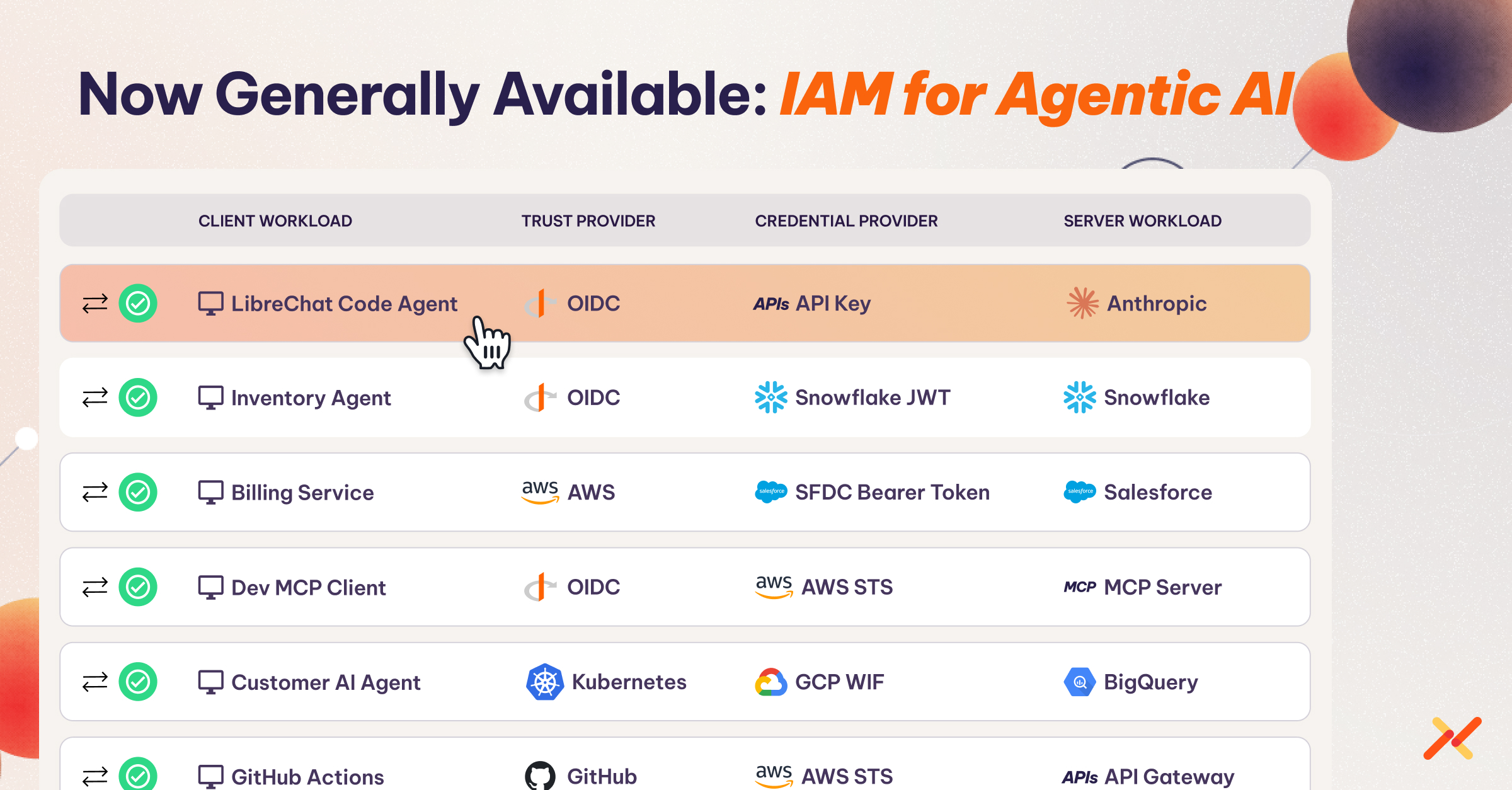
Different platforms use different mechanisms to validate identity. Cloud IAM systems often rely on built-in workload identities. Some modern identity platforms, including Aembit, use cryptographic attestation to verify the workload and its environment before issuing access. Attestation is one method, not a universal requirement for all secretless systems.
By removing static credentials from the ecosystem, the entire attack surface changes. But organizations must have the identity infrastructure in place to support this approach.
2. It’s Not Either/Or: Where Each Model Fits
Choosing between secrets management and secretless authentication is rarely an all-or-nothing decision. Each approach works best for specific types of credentials.
When Secrets Management Is the Right Tool
Some credentials inherently require a secrets manager because no identity-based integration exists:
- API keys for SaaS providers
- Legacy databases using static passwords
- SSH keys and break-glass emergency access
- Third-party services that only support long-lived secrets
In these situations, storing and rotating secrets centrally is still the most secure and operationally predictable option.
When Secretless Authentication Is the Better Fit
Secretless authentication shines in cloud-native and automated environments where workloads already have identity primitives:
- Service-to-service authentication within clouds
- Kubernetes workloads using service accounts or token projection
- CI/CD pipelines that can federate identity
- Multi-cloud APIs that accept identity tokens through OAuth or OIDC
In these environments, static credentials add operational burden without providing additional security value. AI agents add urgency to this shift. Agentic AI workloads spin up dynamically, call multiple APIs per task, and operate across trust boundaries that change by the minute, making static credentials both impractical and dangerous at that scale.
Most Organizations Land in a Hybrid Model
A hybrid model, secretless for modern workloads, secrets management for legacy or external systems, is how most enterprises will operate for years. Secretless authentication reduces the number of secrets you must protect, while secrets management ensures the remaining ones are governed consistently.
Surface area shrinks. Risk shrinks. Operational overhead shrinks. But compatibility is maintained.
3. Capabilities and Limitations of Both Models
Secrets management is strongest when static credentials are unavoidable. It centralizes storage, enforces access controls, automates rotation, and creates the audit trails regulators expect. These capabilities reduce exposure from hardcoded credentials and support legacy systems that cannot authenticate using identity-based methods.
Its limitations, however, stem from the nature of static credentials themselves. Applications still need a bootstrap credential to reach the vault, leaving the secret-zero problem unresolved. Credentials remain viable targets for attackers until rotated. Rotation introduces operational complexity, and vault availability becomes a dependency for every downstream service. As the environment grows, the number of secrets grows with it, increasing management overhead.
Secretless authentication addresses those weaknesses by removing static credentials from the ecosystem. Workloads authenticate using identity, receive short-lived and narrowly scoped credentials, and operate without storing anything long-lived. This dramatically reduces the blast radius of a compromise and simplifies the developer experience by eliminating credential-handling code. Policies can be enforced in real time across clouds and pipelines.
Secretless models bring their own constraints. They rely on uninterrupted identity infrastructure, require precise policy definitions, and are not yet supported by all systems, especially SaaS APIs and legacy databases that still depend on static keys. Some workloads may need refactoring to participate in identity-based authentication. In short, secretless reduces risk but increases reliance on modern identity foundations.
4. Operational Realities: What Teams Experience Daily
Both approaches promise to simplify security, but they shift where the complexity sits.
Developer Experience
With secrets management, developers write credential-fetching logic, handle rotation failures, and maintain separate configurations for every environment. Pipelines frequently break when a credential expires. New microservices require credential provisioning before any feature work begins.
With secretless authentication, developers write no authentication code. The platform injects valid credentials at runtime or uses brokered identity-based access. Deployments no longer trigger credential updates, and rotation is invisible to developers.
Operations and SRE
Secrets management creates ongoing operational overhead. Vault clusters must be maintained, HA must be ensured, rotation windows must be coordinated, and every added service increases administrative complexity.
Secretless platforms shift work from reactive credential maintenance to proactive policy governance. There are fewer emergency rotations and fewer late-night credential outages, but higher reliance on identity services and policy planning.
Security and Compliance
Secrets management improves auditability but keeps credentials in scope. Logs focus on who accessed which secret and when it was rotated.
Secretless authentication focuses audits on identity assertions, policy decisions, and runtime access patterns. Because fewer credentials exist, compliance reviews often focus on policy governance rather than credential hygiene.
5. Risk Posture: Two Very Different Models
Secrets management reduces but does not eliminate credential risk. Attackers target vault tokens, extract secrets from memory, scrape logs, or compromise CI/CD systems. Static credentials remain valid until the next rotation, giving attackers a broader window for exploitation.
These risks compound as organizations deploy AI agents that autonomously call dozens of APIs, each requiring its own credentials. A single compromised agent with hardcoded keys doesn’t just expose one service; it exposes every service the agent can reach.
Secretless authentication removes the static credential entirely. A compromised workload cannot reveal a password because none exists. The primary risks shift to identity infrastructure outages or policy misconfigurations. The blast radius typically shrinks to a single workload instance or session.
Both models reduce different kinds of risk. Secrets management reduces surface area; secretless architectures change the surface entirely.
6. Cost Considerations
The financial differences between the two models become clear as environments scale.
Secrets Management Costs
- Vault infrastructure, backups, and disaster recovery
- Ongoing administration for policy updates, monitoring, and rotation
- Developer time spent writing and maintaining credential plumbing
- Operational burden during large-scale emergency rotations
Secretless Authentication Costs
Most of the investment occurs upfront:
- Deploying workload identity or federation
- Modernizing applications that depend on static secrets
- Training teams on identity-first patterns
- Establishing centralized policy governance
Over time, the cost curve flattens. Rotation disappears. Per-service onboarding becomes easier. And emergency credential resets become rare.
7. Compliance Considerations
Compliance frameworks heavily influence how organizations treat machine credentials, but their requirements have evolved significantly. PCI DSS 4.0’s Requirement 8.6.3, which became mandatory after March 31, 2025, requires that passwords and passphrases for application and system accounts be changed periodically, with the frequency determined by a targeted risk analysis. This replaced the older assumption of fixed quarterly rotation with a risk-based approach. Organizations must still rotate credentials for service accounts, API keys, and other nonhuman identities, but the cadence is now tied to assessed risk rather than a rigid calendar.
This shift matters because it opens the door to smarter credential governance. Organizations that reduce the number of static credentials through secretless patterns have fewer credentials subject to 8.6.3’s rotation requirements in the first place. For the credentials that remain, risk-based rotation replaces blanket schedules, reducing operational burden. Moving toward identity-first access simplifies the compliance narrative further by replacing periodic rotation with continuous identity verification for modern workloads.
Secretless authentication does not remove compliance obligations; it changes their shape. Instead of proving that a password was updated every 90 days, teams demonstrate that no static credential existed and that every access was tied to a verified workload identity.
8. A Practical Decision Framework
A clean way to decide where to invest is to evaluate four dimensions.
Infrastructure Maturity
- Cloud-native architectures benefit most from secretless approaches.
- Legacy or monolithic environments will rely heavily on secrets management.
Risk Tolerance
- Eliminating attack vectors provides transformational risk reduction.
- Some organizations prefer incremental improvements through better governance.
Compliance Requirements
- Secretless architectures simplify some compliance narratives by removing persistent credentials.
- Secrets management offers mature, auditor-friendly trails for regulated environments.
Team Capability
- Secretless adoption requires comfort with identity, policy, and workload security.
- Secrets management aligns with existing operational models.
For most organizations, the correct strategy is phased adoption: start secretless where identity is strong and rely on secrets management everywhere else.
9. The Strategic Investment Decision
Secrets management and secrets elimination are not competing fads; they are two tools designed for two eras of architecture. Secrets management strengthens what already exists. Secretless authentication prepares teams for cloud-native, automated environments where workloads, not humans, drive the majority of access.
The most resilient organizations combine both: reduce secrets wherever possible, manage the unavoidable ones securely, and move steadily toward identity-backed, just-in-time access.
Aembit’s Workload IAM platform enables this transition by providing identity federation, policy-based access control, and secretless authentication for modern workloads while coexisting with the secrets managers you already use.