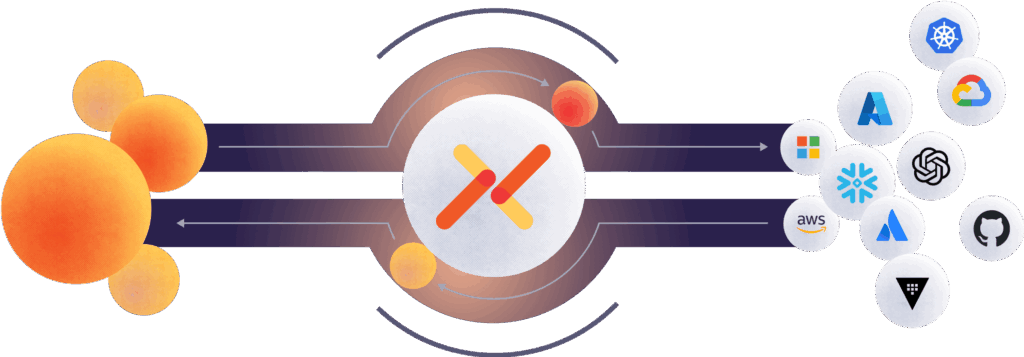
6 min readInstead of duplicating accounts or sharing credentials, one identity system can validate identities issued by another and grant access based on that trust.
Get started in minutes, with no sales calls required. Our free- forever tier is just a click away.